Valtix vs. Aviatrix
Egress Filtering
Critical Capabilities Report
Compare Valtix to Aviatrix Egress Filtering in this critical capabilities report.
Elevate Your Cloud Security in 10 Minutes
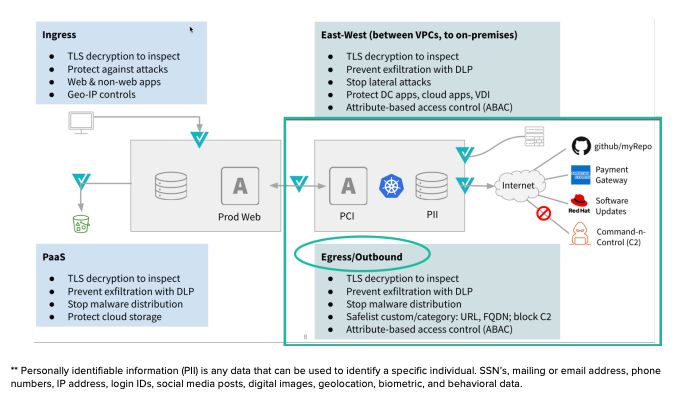
Egress security in the public cloud comprises a significant portion of the total security posture toward protecting public cloud workloads. Questions arise as to what is adequate, good, better, and best when protecting the applications requiring egress to public internet and limiting the “blast radius” in the event of a security breach.
- Where am I vulnerable?
- Is FQDN, or URL, filtering better?
- Should I care about Data Loss Prevention (DLP)?
- Should I deploy a proxy?
- Maybe I need Malware detection also?
- How can I determine if my data is compromised?
- What are my workloads really accessing and why?
Compare Valtix to Aviatrix egress filtering and cloud firewall in this critical capabilities report.
| Functions | NAT Gateway | Squid Proxy1 | Aviatrix FQDN | Valtix Egress |
|---|---|---|---|---|
| Security | ||||
| URL Filtering* | 
|

|

|

|
| FQDN Filtering** | 
|

|

|

|
| Forward/Reverse Proxy (as needed) | 
|

|

|

|
| Custom Lists for Domain Category | 
|

|

|

|
| Auto-Scaling | 
|

|

|

|
| Auto Discovery (App-Tag-based) | 
|

|

|

|
| Auto Malware Detection | 
|

|

|

|
| Data Loss Prevention (DLP) | 
|

|

|

|
| Application Tagging | 
|

|

|

|
| Flow Log Visibility | 
|

|

|

|
| Multi AZ High Availability | 
|

|

|

|
| Allowed/Denied Session Logs | 
|

|

|

|
| Automation and Management | ||||
| Terraform Support | 
|

|

|

|
| API Support | 
|

|

|

|
| Managed Service (SaaS) | 
|

|

|

|
| Enterprise Support | 
|

|

|

|
Valtix Awards

Winner 2022 Stratus Awards “Cloud Company”

Winner “Network Security” Category

Winner “Most Comprehensive Cloud Security”

Gold Winner Hot Security Company of the Year

Cybersecurity Excellence Awards

Winner of “Top 10 Baby Black Unicorns”

Selected as 2021 SINET16 Innovator

Gartner Cool Vendor in Cloud Networking
Compliance Certifications