Article
What is Cloud Network Security?
Recommended
Have Questions? Want to see Valtix in action?
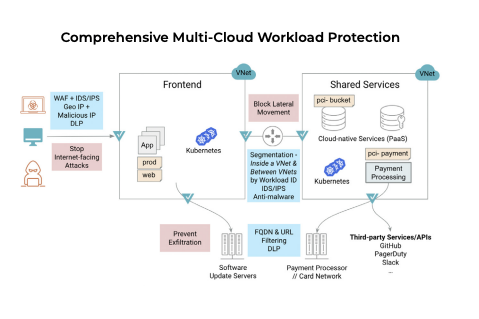
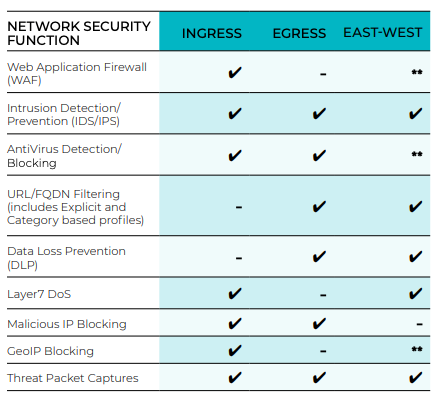
Cloud network security is an essential component of cloud security architecture and encompasses critical security infrastructure such as cloud firewalls, IDS/IPS, FQDN / URL Filtering (Egress Security), Web Application Firewall (WAF), Layer7 DoS, Threat Packet Capture, IP Blocking, and network-based Data Loss Prevention (DLP). With cloud network security, the intent is to ultimately protect application workloads and access to sensitive data.
Cloud network security diminishes the chances of threat actors accessing, changing, or destroying the sensitive information stored in the public cloud. Cloud network security is independent of the underlying infrastructure and therefore provides a consistent way to secure every workload and makes it possible to apply consistent security policies. Cloud network security is a key enabler of defense in depth and least privilege access (Zero Trust).
For cloud network security, we break down the requirements into different network segment functionalities:
- Ingress. This network segment includes any external access to your cloud deployment. Some examples include general public access to a website or application, partner access to an API Gateway, or an on-premises connection to a cloud storage service. The direction is inbound and client-initiated.
- Egress. This network segment covers what your cloud deployment needs to access to perform an operation or function. Some examples may include accessing payment gateways, developer APIs, SaaS services, software repositories, or external URLs hosted on the internet. The direction is outbound and initiated on the application side.
- East-West. This network segment describes the lateral movement within the cloud environment itself. This includes communications such as inter-VPC/VNet, inter-region, endpoint services, private links, or PaaS constructs. These can be either client or server-initiated.
Contents:
In this article, you will learn about cloud network security, including:
Cloud Network Security Platform (CNSP)
A newer category of cloud security, CNSP offers security capabilities as a cloud service. The solution can provide an abstraction layer that simplifies multi-cloud security with a unified management console so you can apply one policy across multiple clouds.
Additionally, CNSP offers full visibility of security events across a complex environment with correlation to specific applications and policies. An agentless solution, CNSP delivers asset discovery, network protection (cloud firewall, IDS/IPS, DLP, egress filtering), and web protection (cloud WAF, DOS). It:
- defends your organization against threats that require east-west movement, such as ransomware
- detects malicious behaviors based on attack patterns
- prevents data exfiltration
Why You Need Network Security in the Cloud
Network security is critical in the cloud because it gives you proactive security that is independent of the underlying application infrastructure or cloud provider. While you also need compliance and governance tools, along with continuous cloud monitoring, those solutions won’t protect you against real-time attacks or data exfiltration.
Pros:
Advantages of cloud network security include:
- Cloud network security is independent of the underlying application infrastructure (containers, VMs, etc.) and therefore, provides a common point of security and consistent multi-cloud architecture.
- Network security techniques such as network-based segmentation, web app firewall, and intrusion prevention provide a strong defense against the exploitation of vulnerabilities.
- Allows implementing context-aware security based on the workload
identity.
Cons:
Disadvantages of cloud network security include:
- Virtual appliance-based solutions may be complicated and time-consuming to implement correctly.
- Each cloud provider makes cloud network security services available, but these can be complicated and costly to implement. They also are specific to that cloud provider, thus being prohibitive for multi-cloud.
Taking a Comprehensive Approach to Cloud Network Security
In the past, the purpose of network security was to secure the network itself, and applications simply inherited that security. But, as recent events have demonstrated, you need to approach cloud architecture differently — and protect the applications regardless of the underlying infrastructure. That’s where network-based controls come in to provide the additional layer of security for your cloud workloads.
This is also required for meeting common compliance and regulatory frameworks such as ISO, SOC, and PCI DSS. A comprehensive approach to cloud network security requires in-depth defense and a combination of passive and active defenses. But to keep up with the cloud’s dynamic environment, the controls must be automated while constantly learning from, and adapting to, the environment.
Six Critical Components of Cloud Security:
Visibility into assets, traffic, and activity — providing visibility into both security posture (e.g., exposed workloads, open network paths, vulnerabilities) and network activities (e.g., exfiltration, lateral movements and attacks, communication patterns)
Infrastructure-as-code (IaC) — eliminating manual processes and automatically integrating security into the deployment cycle (e.g., into tools like Terraform)
Elastic scale — scaling security capabilities automatically along with the cloud workloads they’re protecting, without the need for complex logic of different parameters and thresholds. Security should scale the same way compute, networking, and storage scales.
Identity and context (workload and user) — integrating dynamic asset discovery and tagging in near-real time to automatically identify and contextualize information for cloud assets (eliminating ineffective, broad security policies)
Self-healing security infrastructure — automatically identifying failures and autonomously remediating them to quickly solve problems when vulnerabilities are found, or something breaks down in the cloud security infrastructure
Multi-cloud support — eliminating the complexities of separately managing each cloud’s security, as well as reducing the cost to train for each provider’s security architecture
Architectural Considerations for Cloud Security
There’s no “one size fits all” model for architecting cloud network security. To implement a control point between cloud workloads and the public internet, you can use a centralized, distributed, or hybrid model. Although centralized control and enforcement sounds good in principle, it’s not always the best approach.
For example, centralized control with distributed (or local) enforcement may work better in many cases because it avoids sending traffic across trust boundaries to secure it. Some applications may also require more isolation for compliance reasons. That’s why it’s important to understand the benefits and drawbacks of each approach before choosing the best combination for your environment.
Centralized control:
Provides global definition and management of policy across large multi-cloud deployments. This model enables you to define consistent policies regardless of where the application is located; it also provides visibility for all types of security events. Avoid single point of failure of legacy architectures by implementing centralized controls with cloud-native design patterns — including multi-availability-zone (AZ) and multi-region architecture, along with elastic cloud-native services.
Distributed control:
Spans across different security appliances that must be integrated to work together. This enables more granular security controls, but it also lowers your visibility across multiple clouds and creates redundancies or inconsistencies. Management and support costs also go up in this model.
Centralized enforcement:
Routing all traffic to a central point provides consistent policy enforcement, but also introduces compliance issues and creates inefficiencies.
Distributed enforcement:
Keeps traffic close to the application for local enforcement, enabling you to define policies for specific application requirements and enforce policies quickly and reliably, but it can be difficult to operationalize at scale.
Valtix’s Solution to Cloud Network Security
Valtix simplifies cloud network security, delivering advanced network protection (cloud firewall) built to secure your multi-cloud applications, infrastructure, services, and APIs native to public cloud (AWS, Azure, GCP, OCI). Secure ingress, egress, and east-west traffic to detect and stop malicious or prohibited activity across every account, VPC, and cloud provider network.
Bottom Line:
Cloud Network Security Platform (CNSP) complements other solutions, including Cloud Security Posture Management (CSPM), by adding protection against other serious threats to give you a complete stack for securing apps and workloads. A third-party, cloud-native CNSP overcomes the technology challenges of virtual appliance-based or cloud provider-specific services to offer robust, layered defenses, along with fast deployment that takes only a few minutes across a multi-cloud infrastructure.