Cloud Web Application Firewall (WAF)
Simple-To-Deploy, Integrated Cloud Web Protection
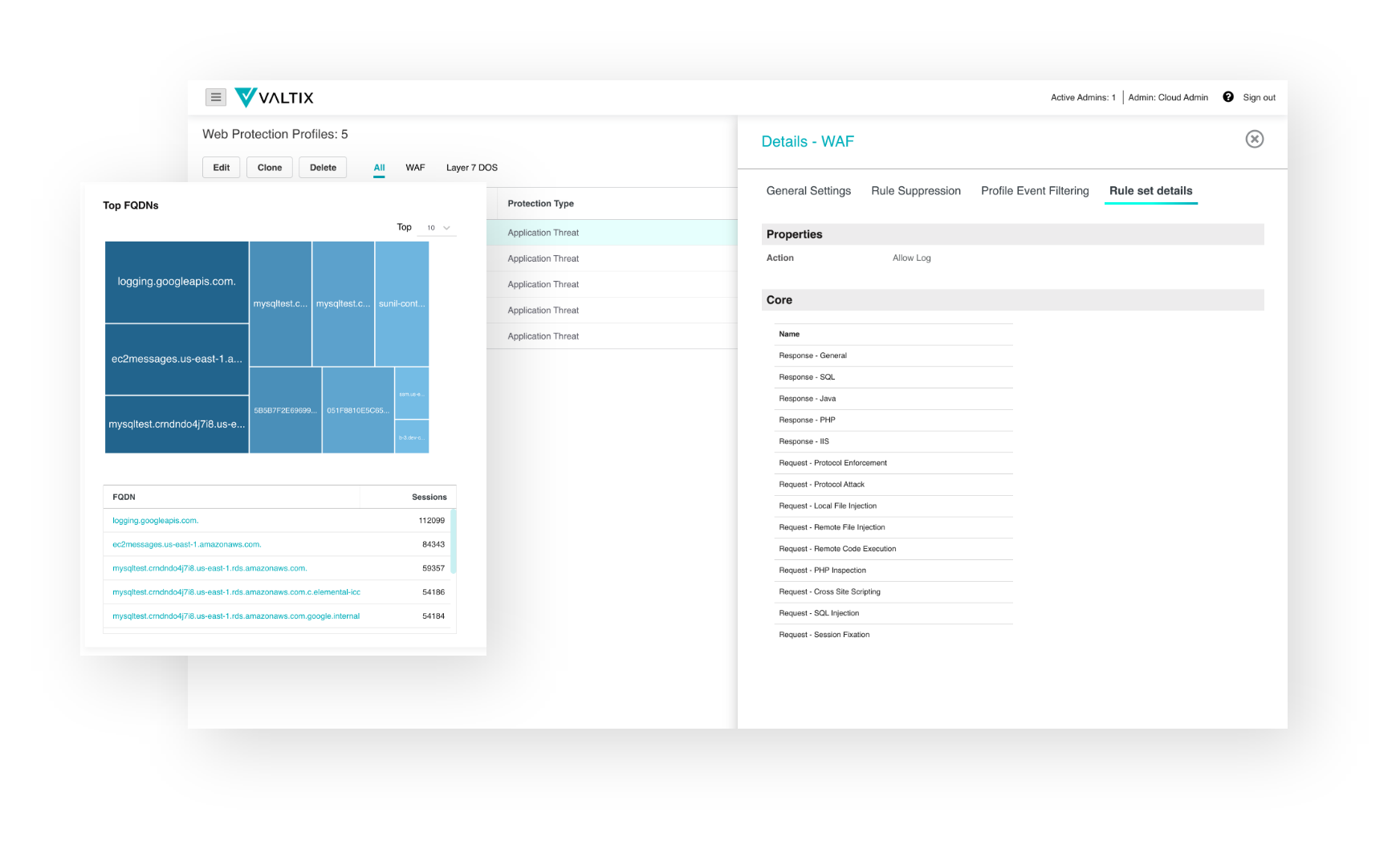
Valtix delivers cloud web application firewall (WAF) for AWS, Azure, GCP (Google), and OCI (Oracle) to secure your web applications and APIs against external threats. Unlike other cloud WAF solutions, our integrated platform enables WAF deployment and management within your organization’s environment alongside other security controls such as NGFW, IDS, and DLP. The result: better security through a single policy framework for cloud network security.
Secure Web
Apps and APIs
Cloud WAF is essential to stop attacks in the 90% of all traffic that is HTTP and HTTPS
Advanced
Protection and Rule Sets
Enterprise-grade cloud WAF with OWASP Top 10, core rule set (CRS), and advanced application-specific rule sets
Block
Denial of Service
API Rate Limiting, malicious IP threat intelligence, and geographic IP policies combine to help prevent attacks
Simplify to Improve and Reduce Costs for Cloud WAF
According to the annual Verizon Data Breach Investigations Report, 43% of attacks involve web applications. Only Valtix delivers cloud Web Application Firewall (WAF) for comprehensive security against attacks from the internet (ingress) along with data exfiltration (egress) and lateral movement (east-west). Instead of point solutions that cover only individual use cases, Valtix cloud WAF provides a single pane of glass for traffic flows across the entire kill chain.
“Valtix uses a SaaS Controller to enormously simplify deployment of network security in our public cloud. Life is easier with Valtix and we can now focus more on business outcomes.”
Director of Public Cloud Architecture FinServ Bank
Enables a Robust Defense Against External Threats
Cloud Web Application Firewall (WAF)
Valtix provides an integrated, multi-cloud security platform that drastically simplifies and improves management and security. Includes built-in auto-scaling and continuous threat signature updates.
Advanced Security Rule Sets
Defend against vulnerability exploits with the latest threats OWASP Top 10 protection and advanced cloud Web Application Firewall rulesets.
API Rate Limiting to Limit DoS
Protect sensitive URLs and API endpoints with customized rules that ensure that attackers cannot exploit and overload your applications.
Integrated Threat Intelligence on Malicious IP
Continuous updates on malicious IPs from our threat intelligence team and the option to add custom feeds ensure your web applications are protected against known bad actors.
Geolocation of IP Addresses
Valtix Cloud WAF provides visibility into the source countries and configures controls to restrict access using GeoIP-based policies.
Is Your Cloud Infrastructure Secure?
Learn Best Practices in Cloud Network Security