Valtix 2.9 is a significant release that revamps how organizations can secure their public cloud IaaS and PaaS deployments. And, as always for a SaaS, Valtix Controller aka portal updates are transparent and Valtix Gateway updates just take 1-click, hitless with a blue-green that takes minutes.
Here’s a quick rundown of the features:
-
- Easy Setup – 5-minute steps for a variety of tasks: onboard cloud accounts and enable discovery, build a hub-n-spoke setup, and deploy auto-scaling Gateways
- Multi-Cloud PaaS Visibility & Control – Protect the 100s of cloud services from AWS, Azure, and Google Cloud using Valtix Gateways
- Flexible Multi-Cloud & Multi-Account Dynamic Security Policies – Build truly multi-cloud and multi-account policies that adapt to changes in your infrastructure
- Group Address Objects – Build policies with more complex address objects
- Protect Unsecured VPCs – Quickly review unprotected VPCs and add them to a hub-n-spoke setup
- Cloud Visibility Report (CVR) Threats Indicators Snapshot – Create a quick executive summary from Gateway traffic and threat logs
- Visibility of Out-of-band Traffic in Azure and Google Cloud – detect indicators of compromise (IoC) to determine which instances and VPCs are connecting to malicious IPs/sites
- New Navigation Menu & Search – All menus are now located on the left-side with a list of recently used items and search is available across address objects, policies, and the left-side menu itself
- Terraform Improvements – customer-requested enhancements and verified status
You can find the release note and documentation here: docs.valtix.com/releases/2.9/features_changes/
I’ll give you a quick rundown here, though.
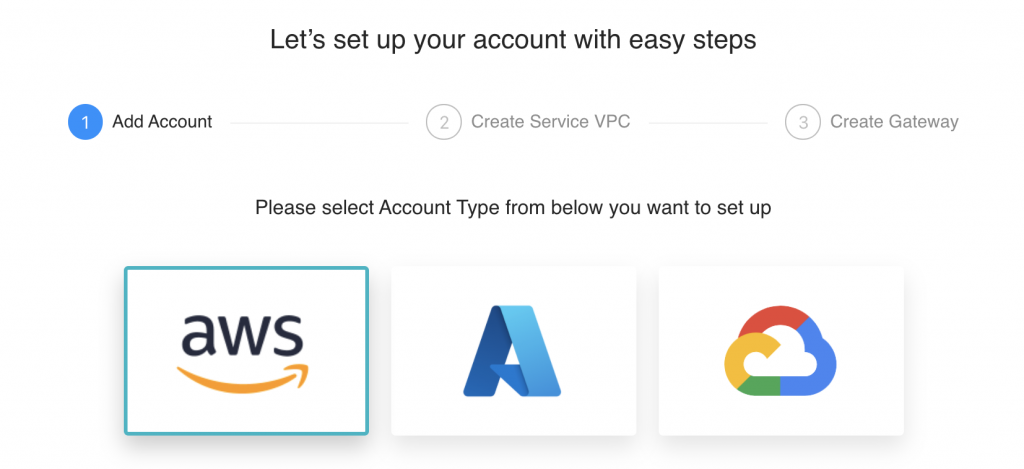
Easy Setup in 5 Minutes, The Cloud-Native Way
To simplify the task of deployment and day-to-day operations we’re introducing 5-minute steps for a variety of tasks. This release starts with easy setups for common AWS scenarios. Future releases will add support for Azure and Google Cloud. Advanced scenarios like cross-account hub-n-spoke or onboarding of 10s of cloud accounts can still be managed through existing workflows in the Valtix portal or the Terraform provider for Valtix. These steps follow the discover, deploy and defend workflow pioneered by Valtix.
- Onboard Cloud Accounts – add your cloud accounts, review the discovered asset inventory, review the DNS queries and VPC flow logs to find out if any of your instances or VPCs are compromised or connecting to malicious IPs and sites.
- Build a hub-n-spoke setup – add your spoke/application VPCs with a few clicks to a security hub aka Services VPC with full AWS Transit Gateway automation.
- Deploy Valtix Gateways – setup Valtix Gateways with built-in auto-scaling in the Services VPC. This uses the AWS Gateway Load Balancer behind the scenes, but you don’t need to worry about the deployment details – Valtix simplifies the entire setup for you.
Easy setup in Valtix makes it simple to deploy and manage robust network security to protect your workloads.
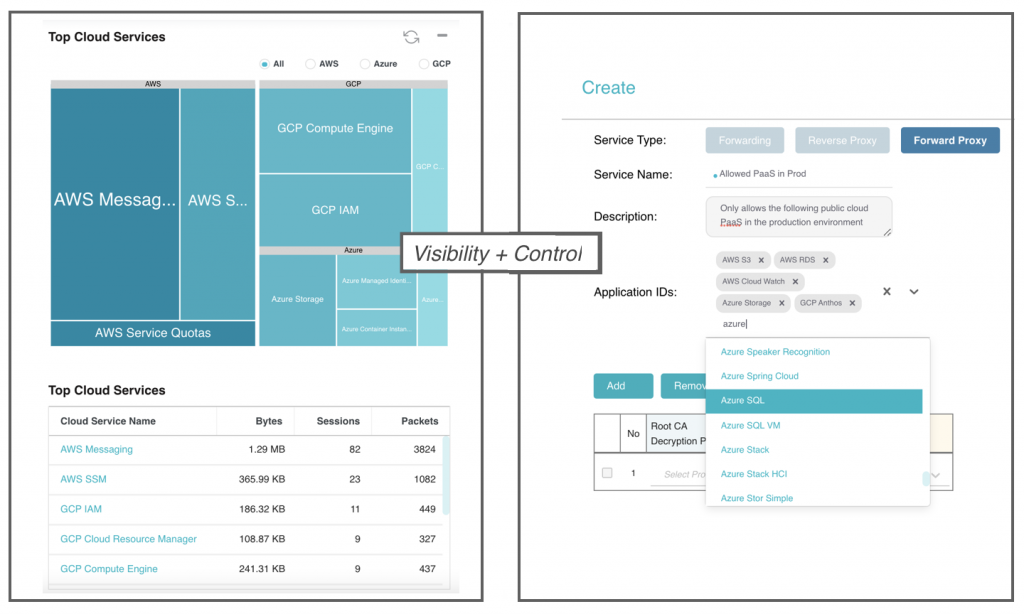
Multi-Cloud PaaS Visibility & Control
Whether you’re migrating from on-prem hosting or building cloud-native applications, cloud services are the fundamental building blocks, from AWS S3 buckets and RDS, to Azure SQL to GKE on Google Cloud. Unfortunately, it’s easy to misconfigure them or have inappropriate access from malicious insiders. While cloud security posture management (CSPM) tools and cloud-native options like AWS Config do help, they are not sufficient as proven by the numerous public cloud exfiltration incidents we’ve seen recently.
Valtix Gateways bring a defense in depth approach, first is visibility and then control of the 100s of cloud services (PaaS) available across the major clouds. None of the traditional NGFWs have any visibility of the 100s of PaaS available across each cloud provider. Simply deploy Valtix Gateways in your AWS, Azure, or GCP environment and get deep visibility, and then configure explicit policies that can:
- Allow “dev” workloads to use all AWS PaaS offerings
- Restrict “prod” and “compliance” workloads to only use approved list of Azure PaaS
- Find out why “pci” workloads are connecting to unapproved DynamoDB instances
- Get visibility if malware is being stored in your GCP storage and which instances and VPCs are connected to it
- Set DLP policies to ensure credit cardholder data (CHD) is not stored in raw format in your databases to meet PCI-DSS compliance requirements.
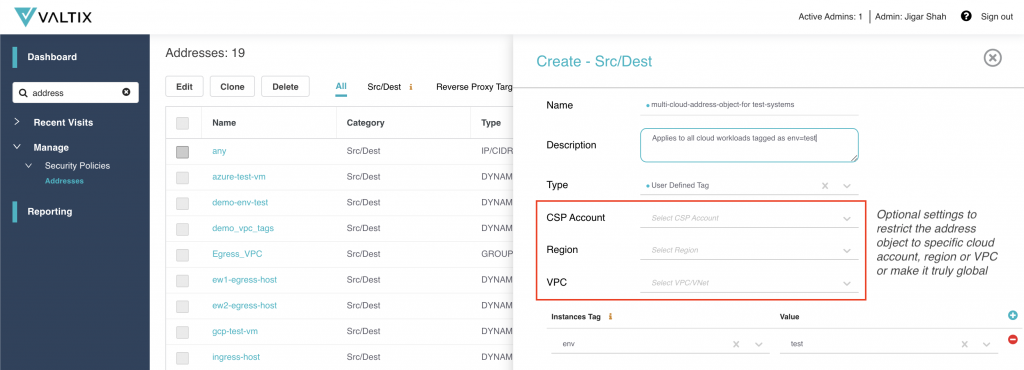
Flexible Multi-Cloud & Multi-Account Dynamic Security Policies
To truly protect your public cloud workloads, network security must continuously adapt to changes in your environment: auto-scaling instances, add/remove/change of instances, VPCs and accounts. Without continuous discovery, whether it’s 10 VPCs or 100s, and 100 instances or 1000s, it’s practically impossible to protect them. Valtix uses its continuous discovery to not just bring visibility, but also enable creating dynamic policies across cloud accounts (in the same cloud) and for all clouds.
Release 2.9 brings flexibility in how you pick the asset properties (pre-defined values and 10s/100s of user-defined tags) to define address groups and security policies. Now, the tags can be restricted to a particular cloud or account or can apply across clouds and across accounts. This flexibility allows the security team to quickly pre-build all the security policies and as workloads come and go, they are automatically protected. Here are some example policies:
- Allow “dev” workloads in any account, any cloud to connect to all of github.com/*
- Allow “prod” workloads in any cloud account, and/or any cloud to only connect to a specific URL/FQDN category or specific sites like github.com/myOrgRepo
- Restrict “pci” workloads in AWS to connect to approved AWS PaaS
From a security perspective, this ability to create multi-cloud and multi-account policies driven by the continuous discovery of cloud assets is what truly protects your cloud deployments. You can now build zero-trust policies in minutes, not days, without needing to create tickets for each and every application for each VPC, account, and cloud. And it’s designed to work at scale, for 10s and 100s of VPCs and 1000s of instances. Try that with your legacy next-generation firewall (NGFW).
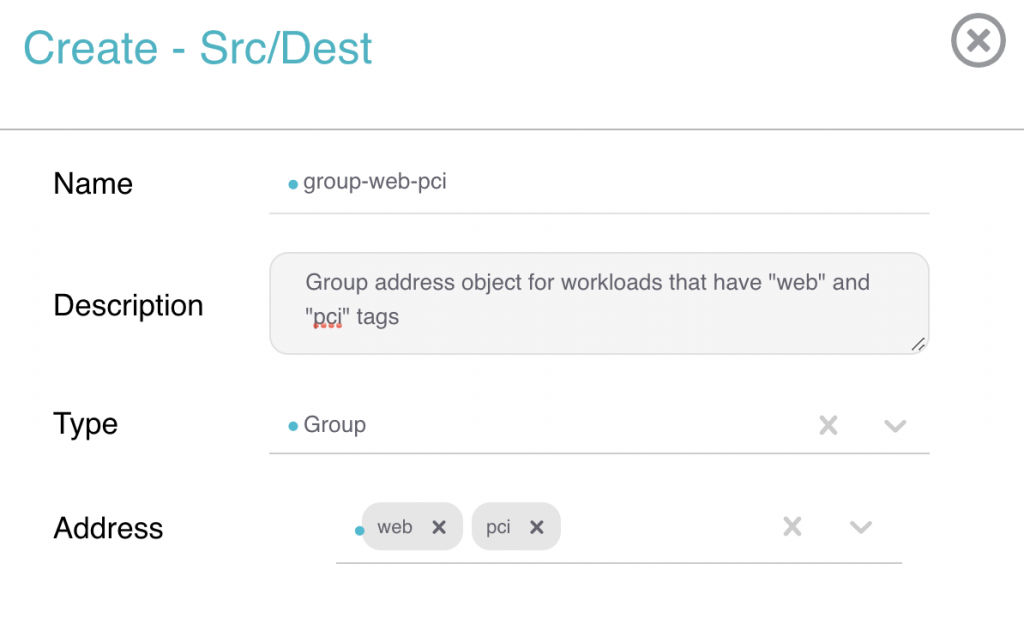
Group Address Objects
To make it easier to build dynamic multi-cloud policies you can now build Address Objects using multiple tags, for example, all workloads with “web” and “pci” tags.
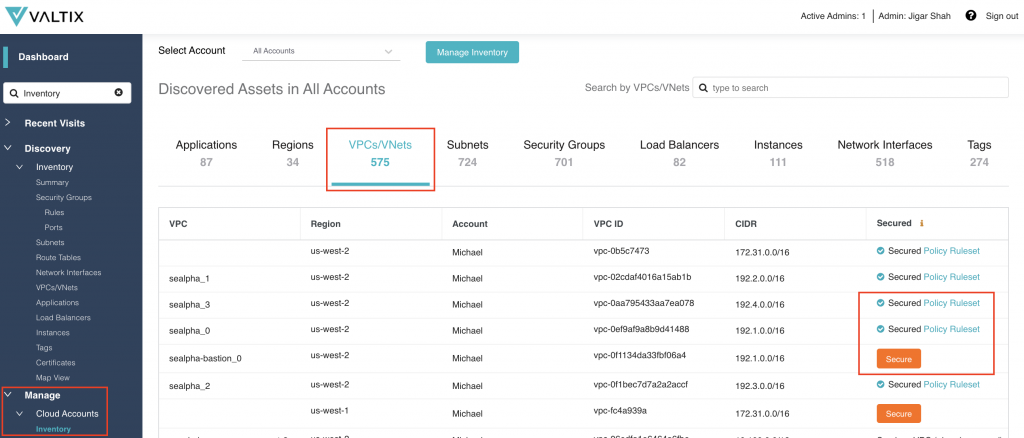
Protect Unsecured VPCs
This feature alone would be their headline announcement for any other security product. Valtix is now making it easy for cloud operations and security administrators to detect which VPCs are secured and which ones are not. And, then with one click, select a policy to protect it as a spoke VPC connected to a services VPC running Valtix Gateways. To review your VPC status go to Manage > Cloud Accounts > Inventory > VPCs (or just search for “Inventory”).
Cloud Risk Assessment Report
Valtix now provides a summary of traffic and threats seen by Valtix Gateways. The CVR Threat Indicators Report provides a continuous report of the value Valtix provides in protecting your public cloud deployment. You can also save the results as a PDF report. The CVR Threat report complements the CVR Discovery report which is based on the out-of-band traffic of DNS queries and VPC flow logs, correlated with cloud asset information and threat intelligence.
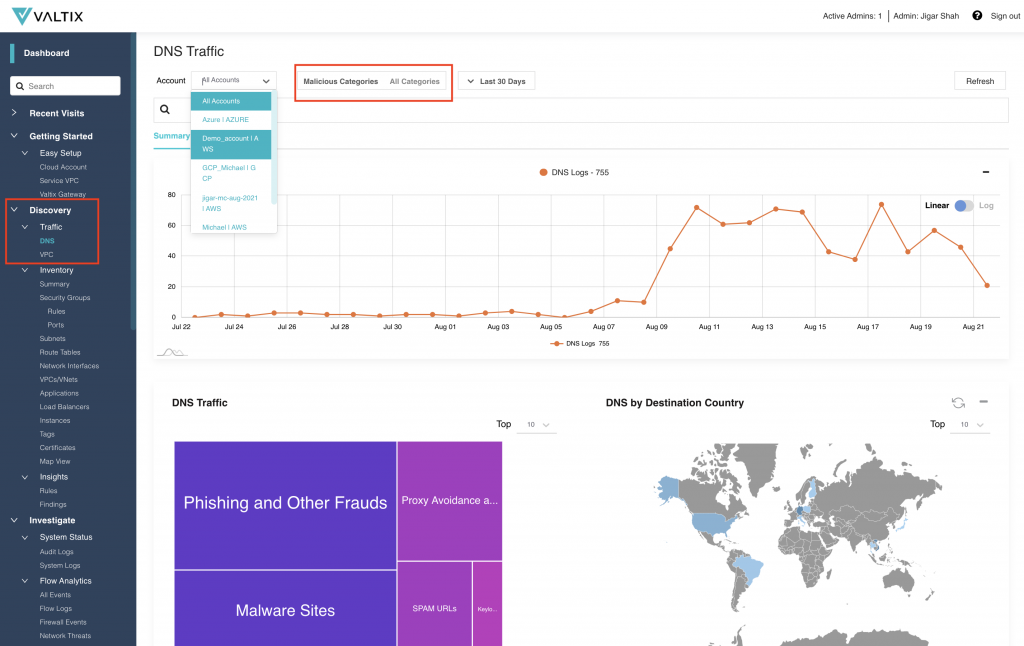
Visibility of Out-of-band Traffic in Azure and Google Cloud
Valtix already supports out of band traffic of AWS Route 53 DNS queries and VPC flow logs. This release adds support for:
- Azure VNET traffic activity
- Google Cloud DNS queries and VPC flow logs
Visibility into DNS and VPC Flow logs can’t be understated. This data, combined with cloud asset information and threat intelligence, provides a critical security data point on which instances and VPCs might be compromised. It enables security administrators to detect exfiltration attempts on outbound/egress traffic to malicious IPs and malicious sites. And with a couple of clicks, you can investigate detailed logs and decide on further incident response actions. Now its clear which VPCs and workloads need to be protected first with Valtix Gateways.
New Navigation Menu & Search
All menus are now located on the left-side with a list of recently used items. Also, search is now available across address objects, policies, and the left-side menu itself. This makes it easy for admins of large Valtix deployments to find the exact address objects and policy they want to edit.
Terraform Improvements
The Terraform provider for Valtix has now officially reached verified status. We’ve made a few improvements and bug fixes based on customer feedback to improve infrastructure-as-a-code (IaC) automation to bake security into their DevOps process.
- Support for new features in v2.9 and v2.8:
- Address Groups
- Valtix Gateway Support for EBS encryption and custom tags
- Flexibility in defining user defined tags
- Improvements
- Bug fixes for Terraform provider on Windows (we also support Mac and Linux)
- Improved error handling
To learn more, please join me next week for our launch webinar. Register here:
https://valtix.com/resources/webinar-valtix-29-multicloud-network-security/