Valtix Reboots Network Visibility for Public Clouds
Public clouds are enabling a new application architecture consisting of IaaS (compute, networking, storage), PaaS (with 10s of services like AWS S3, RDS, CloudWatch), and microservices (including container-based and service mesh). This includes lift and shift VMs, refactored applications and modern cloud-native designs. In addition, applications are also using third-party services like GitHub, Twilio, Slack and others. This variable app architecture means protecting them becomes very challenging. And to protect something, you first need to start with visibility. With this release Valtix is deepening our Discovery features and building on the visibility features we released in January.
These visibility features are available in two ways:
- Just enabling a simple IAM role for Valtix to give you deep insights from AWS Route 53 DNS queries and VPC flow logs. This does not require deploying any Valtix Gateways and is included as a standard feature set of Valtix.
- Deploying Valtix Gateways for actual inline protections against connections to malicious sites such as phishing or command-and-control (C2) and preventing exfiltration.
New Features and Updates in Release 2.7
- Cloud Visibility Report (CVR) – sample PDF
- AWS VPC Flow Log Analytics for Malicious Egress Connections
- Simplified Hub-and-Spoke Design for AWS
- Support of New Regions for AWS Gateway Load Balancer
- MFA Support for Valtix SaaS Portal
- Log Forwarding to Google Cloud Logging (formerly Stackdriver) – requires updating Valtix Gateways
- Log Forwarding to Syslog over TCP
Almost all features, sole exception noted above, in this release are on the Valtix Controller, i.e. available automatically to all customers and don’t require any immediate/urgent updates to the Valtix Gateway. In general, we recommend customers to update their Valtix Gateway software to the latest as we continuously fix bugs and improve our product security continuously. Valtix Gateway updates are hitless (i.e. zero downtime) and take minutes to roll out across your entire Gateway fleet with the typical cloud-native blue-green style update process. To learn more about these features refer to docs.valtix.com/
Cloud Visibility Report
To summarize the discovery and visibility features of Valtix this release provides an ability to generate a summary PDF report for decision makers and security teams. This gives them an insight into network traffic flows in their current AWS environment and helps guide on which inline network security protections might be needed. The current release provides insights into egress (outbound to Internet) traffic flows to determine if your cloud deployment is connecting to malicious sites running command-and-control (C2) or inappropriate sites (adult, phishing, gambling etc), and start an incident response investigation.
Valtix synthesizes the following information in a single pane of glass that lets you see top-level information and an ability to quickly drill down to logs in seconds, and see contextual information (instance level tags) and threat intelligence:
- DNS queries from AWS Route 53 and VPC flow logs
- Continuous, near real-time, inventory of your cloud assets: multiple AWS accounts, regions, VPCs, instances and their meta-data such as tags that identify workloads (“dev”, “prod”, “web”, “pci” etc applied by application teams)
- Threat intelligence on FQDN/domain site categorization (from BrightCloud) and malicious IPs (from Trustwave).
To protect your cloud deployment, you can deploy Valtix Gateways in a simple hub-and-spoke design to quickly secure 10s of your VPCs from a central Valtix security hub per region. This allows you to apply machine-id based cloudaware security policies that apply URL and FQDN filtering, malware inspection (via IDS/IPS and antivirus), and data loss prevention (DLP).
The cloud visibility report is available for free to all prospective customers and existing customers. Contact us to request a demo.
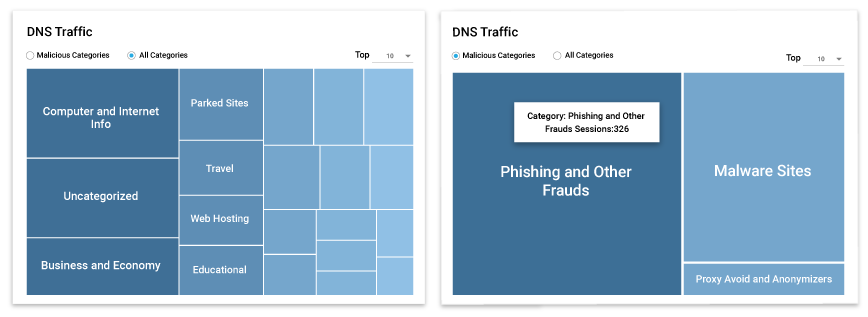
AWS VPC Flow Log Analytics for Malicious Egress Connections
In January, Valtix release v2.6 introduced analytics of DNS queries from AWS Route 53 which enables customers to get visibility traffic to the various egress destinations. This enables insights into the variety of site/domain categories for both benign and malicious destinations. This is combined with cloud asset discovery enabling security administrators to identify potentially compromised instances along with the machine-identity (region, account, VPC, tags).
Now Valtix is expanding this to include analytics for VPC flow logs that provide customers with a 360o view into egress connections. This correlates the traffic against malicious IPs (provided by Trustwave) to identify potentially harmful flows. The summary dashboards break this down across VPCs and instances, and the different ports and protocols for benign versus malicious IP flows. Also, the DNS queries (intent) can now be quickly correlated with VPC flow logs (actual behavior) to determine details of the sessions.

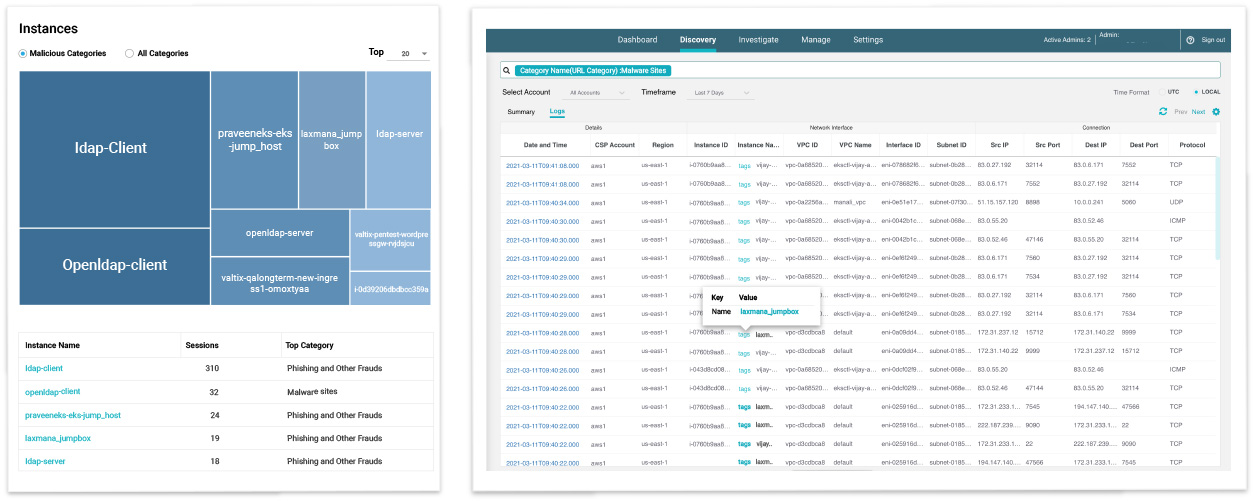
Simplified Hub-and-Spoke Design for AWS
Hub-and-spoke has emerged as one of the most common designs for network security in public clouds. It allows you to quickly secure traffic for 10s of spoke VPCs where applications run, and Valtix Gateways run in a hub VPC which connects to the spokes via the AWS Transit Gateway. This makes it incredibly easy for security teams to quickly protect applications in spoke VPCs and provide a centralized security stack where autoscaling Valtix Gateways are running. This provides a high amount of elastic security while letting application teams have full control inside their VPCs. Valtix Gateways in the security hub can now consistently enforce protections against attacks from the Internet, prevent exfiltration for outbound traffic to the Internet, and stop lateral movement of attacks between VPCs.
Based on customer feedback this release simplifies creation of the security hub (called Services VPC in Valtix portal) and the attached AWS Transit Gateway. The autoscaling Valtix Gateways can then be deployed inside the Services VPC, and then you can just attach all your application spoke VPCs. The previous flow used to combine creation of Valtix Gateways with creation of the AWS Transit Gateways; now it’s separated and very clean – build the AWS networking infrastructure and then Valtix Gateways. Under the covers, the Valtix Security Hub VPC uses the AWS Gateway Load Balancer. Customers don’t need to worry about the setup and operational management of the security hub itself, i.e. you don’t need to maintain your network security infrastructure – its SaaS managed. You simply configure security policies and the rest (discovery, auto scaling, software updates, threat signature updates) is taken care of by Valtix.
To learn more about how customers are using this see how Saxx Underwear protects their public cloud assets with Valtix.
Support of New Regions for AWS Gateway Load Balancer
In early March AWS released support for Gateway Load Balancer (GWLB) in four new regions, adding to the five regions from the initial launch in November 2020. Valtix has now added support for these new regions. As AWS launches support in the remaining regions, we will quickly add them. To learn more about AWS Gateway Load Balancer and how it makes network security in public clouds drastically simple, see here for an overview and a technical deep dive.
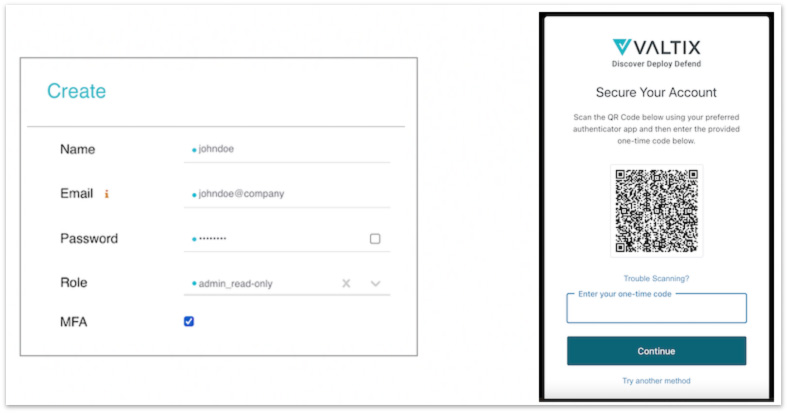
MFA Support for Valtix SaaS Portal
The SaaS portal for Valtix already supports single sign on (SSO) providers like Okta which also support their own multi-factor authentication (MFA). With this release Valtix also directly supports our own MFA for administrators. When logging into Valtix you can use a virtual MFA app like Google Authenticator and others, or receive an email with a one-time code. This setting can be enabled for each user from the Valtix SaaS portal > Settings > Users. Next time the user logs in, they will be required to set up their MFA. Support for receiving the one-time code as a text message (SMS) will be added in the coming weeks.
 {: width=”788″ height=”413″}
{: width=”788″ height=”413″}
Enabling MFA for a Valtix admin user and the first-time login screen for the user
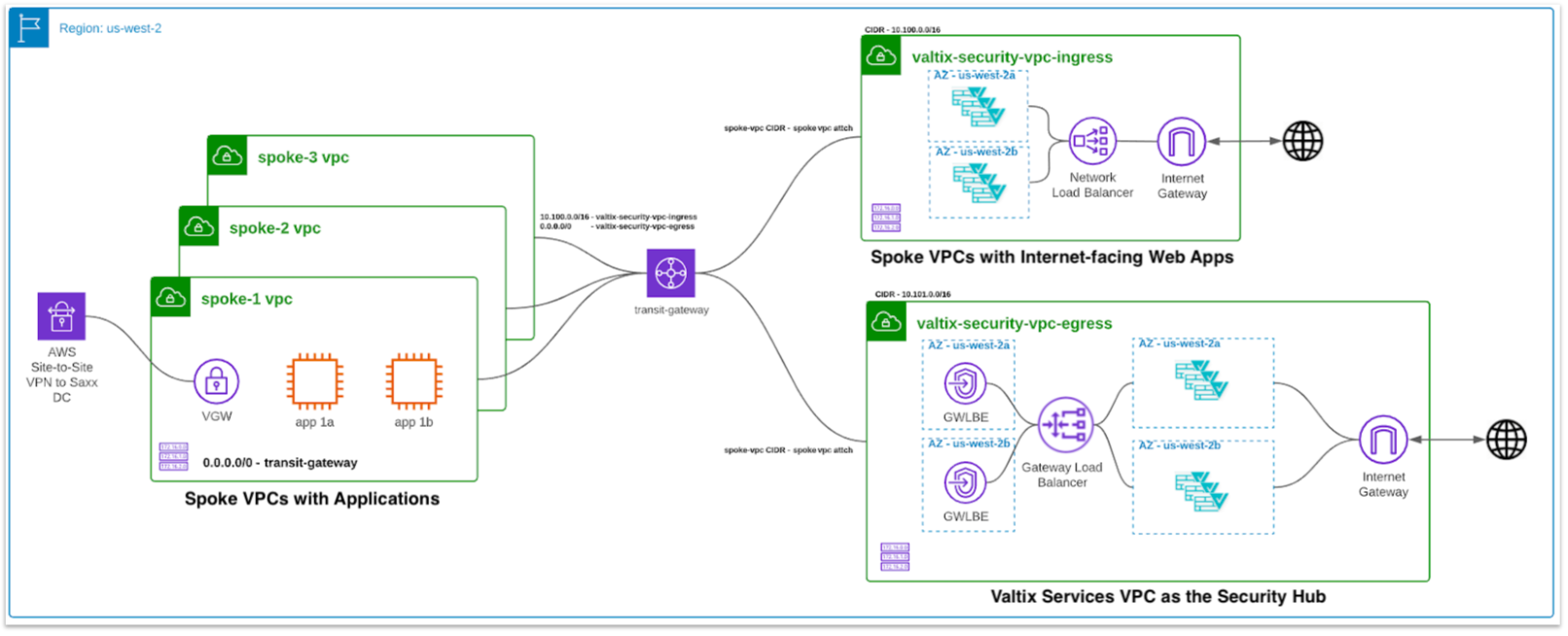
Log Forwarding to Google Cloud Logging (formerly Stackdriver)
Logging is a big deal for networking and security, they help us debug issues, diagnose connectivity issues and find threats/attacks. Valtix currently supports sending traffic and threat logs to syslog, Datadog, and Splunk. And, you can set up alerts from Valtix to be sent to PagerDuty, Slack or ServiceNow. This release adds a new cloud-native option for sending logs to Google Cloud Logging directly from Valtix Gateways running in the customer’s Google Cloud account/project. Log data is sent as a standard JSON payload. This allows customers to perform additional analytics powered by Google Cloud and also save the logs for archival purposes at a significantly lower cost than SIEM tools.
Setup is as easy as ever:
- Setup Google Cloud Logging in your project.
- The IAM role for Valtix Gateways (i.e. the Google Cloud service account for valtix-gateway) should allow Valtix to send logs to your chosen log destination.
- Setup the log forwarding profile in Valtix SaaS portal > Manage > Log Forwarding > Create.
That’s it! Now your Valtix logs start flowing directly into your Google Cloud logs.
Log Forwarding to Syslog over TCP
In addition to sending logs to syslog servers over UDP, you can now chose to send them over TCP. This is part of the Manage > Log Forwarding settings.
To try out Valtix or these new features in your cloud accounts, you can sign up at https://www.valtix.com/trial/ for a free 30 day trial.

 {: width=”788″ height=”413″}
{: width=”788″ height=”413″}